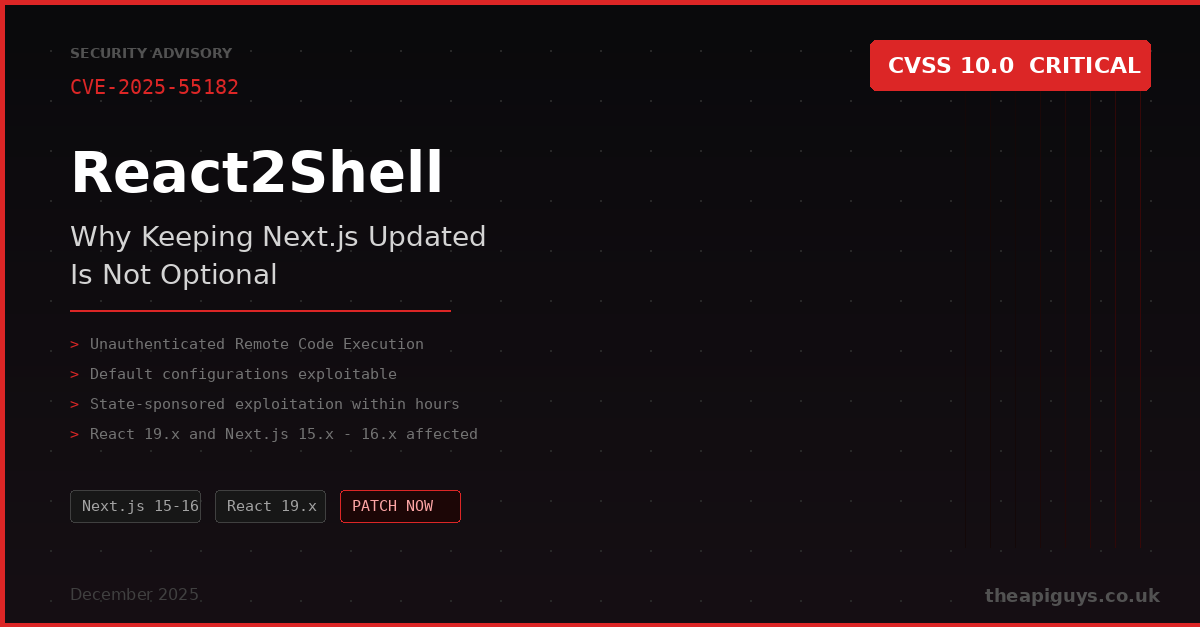
React2Shell - Why Keeping Next.js Updated Is Not Optional
If you are running a Next.js application in production, the events of early December 2025 should serve as a wake-up call. A critical vulnerability dubbed React2Shell was disclosed on 3rd December, and within hours, state-sponsored threat groups were already exploiting it in the wild.
This is not a theoretical risk. It is a real-world example of why keeping your software up to date is not something you can push to next sprint.
What Happened
Security researcher Lachlan Davidson responsibly disclosed CVE-2025-55182 to the React team on 29th November 2025. The vulnerability sits in the React Server Components "Flight" protocol, which is the mechanism React uses to stream component data between the server and the client. It was assigned a CVSS score of 10.0, the maximum possible severity rating.
The flaw is an insecure deserialisation vulnerability. When a server running React Server Components receives a specially crafted HTTP request, it fails to validate the payload structure properly. This allows an attacker to influence server-side execution logic, resulting in unauthenticated remote code execution. One request. No authentication required. Full server access.
Patches were published to npm on 3rd December 2025. A working proof-of-concept exploit appeared publicly within 30 hours of disclosure.
Who Was Affected
The vulnerability affects any application using React 19 Server Components, most notably Next.js applications using the App Router. Critically, even a blank Next.js application scaffolded with create-next-app was exploitable in its default configuration. You did not need to have written any vulnerable code yourself. The framework's default setup was enough.
Next.js versions 15.0.0 through 16.0.6 were affected. The vulnerable React versions included 19.0, 19.1.0, 19.1.1, and 19.2.0 across the react-server-dom-webpack, react-server-dom-parcel, and react-server-dom-turbopack packages.
How Fast It Was Exploited
This is the part that should concern anyone responsible for maintaining production applications. Amazon Web Services reported that within hours of the public disclosure, multiple China-nexus threat groups were actively exploiting the vulnerability. Google Threat Intelligence Group observed distinct campaigns deploying backdoors, tunnelling tools, and cryptocurrency miners. Microsoft confirmed exploitation activity as early as 5th December, with both red team assessments and real-world threat actors delivering payloads across Windows and Linux environments.
The speed of exploitation is staggering but not surprising. When a vulnerability scores 10.0, requires no authentication, and works against default configurations of one of the most popular web frameworks in the world, attackers move fast. The window between disclosure and exploitation is measured in hours, not weeks.
It Did Not Stop There
Following the React2Shell disclosure, further security research into the patched code uncovered two additional vulnerabilities in the same React Server Components protocol. CVE-2025-55184 is a high-severity denial of service vulnerability, and CVE-2025-55183 is a medium-severity source code exposure issue. Neither allows remote code execution, but both require patching. The initial fix for the denial of service was itself incomplete, requiring yet another round of updates.
This cascade of follow-on patches is a familiar pattern. Once a critical vulnerability draws attention to a particular area of code, researchers dig deeper and find more issues. If you patched once on 3rd December and walked away, you may still be vulnerable. Staying current means staying attentive.
What You Should Do
If you are running any Next.js application using the App Router, check your versions immediately. The Next.js team released an interactive tool to help:
npx fix-react2shell-next
This will check your dependency versions and perform the necessary upgrades. The patched Next.js versions at time of writing are 15.0.5, 15.1.9, 15.2.6, 15.3.6, 15.4.8, 15.5.7, and 16.0.7 or later. For React, ensure you are on at least 19.0.4, 19.1.5, or 19.2.4.
Once patched and redeployed, rotate all your application secrets and environment variables. If an attacker gained access before you patched, they could have read everything your application has access to.
WAF rules from providers like Vercel, Cloudflare, and AWS offer an additional layer of defence, but they are not a substitute for patching. Attackers can modify payloads to bypass signature-based blocking. The only reliable fix is upgrading.
The Bigger Picture
React2Shell sits in the same category as Log4Shell before it. A critical vulnerability in a widely adopted component, exploitable in default configurations, with rapid weaponisation by sophisticated threat actors. The parallels are hard to ignore.
This is exactly why we keep talking about the importance of keeping your software stack current. Security vulnerabilities do not wait for convenient moments. They do not care about your sprint planning or your release schedule. When a CVSS 10.0 drops, the clock starts immediately.
If you are running applications on Next.js, React, or any framework for that matter, you need a plan for applying security updates quickly. Not eventually. Not when it is convenient. Quickly. The difference between being compromised and being safe in the React2Shell incident was measured in hours.
If you need help auditing your Next.js applications, planning an upgrade, or putting processes in place to stay on top of security updates, get in touch. This is exactly the kind of thing we help with.